Security groups and network ACL both are widely used when we use AWS as Infrastructure as a service (IaaS). Both security group and network ACL works as firewall, which is basically controlling in-flow and out-flow of some/all traffic
Table of contents
Open Table of contents
Security Groups
Security groups works as filters for your aws computing components. Security group works on instance level.
By default each VPC have security group set with inbound and outbound traffic to ALL (public). Default security group is only assosiated to any component if we do not explicitly associate any security groups
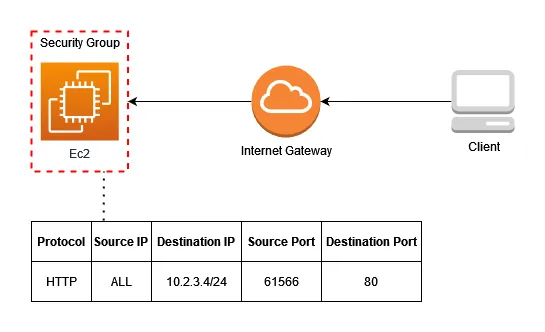
Security groups are stateful firewalls. stateful firewall considers each operation as individual state, we specify inbound rules it will automatically configure outbound rules (inverse values for source and destination entities) for giving back response of the request.
Security groups have similar setting as firewall setting in any windows server, where we can select the type of protocol and range of port at inbound and outbound settings.
when creating security group if we don’t specify inbound and outbound rules, instances with associated security group will have no ingress(entry traffic) or egress(exit traffic) traffic
In security group we can add rules for different type of traffic like TCP, SSH etc
Great thing about security groups is that you can manage a set of resources having same rules to control traffic, No need to configure each resource individually. We can have multiple security group at any instance and also same many instances can use multiple security groups.
Security group doesn’t have DENY rule for any traffic, any other traffic not listed in rules is implicitly denied.It is hard to maintain multiple security groups and resources in an organization, AWS firewall manager is great tool audit and update security groups for your particular network (VPC)
Lets consider a use case for security groups
Imagine a simple app with frontend and backend services along with load balancings
.C39OtuQS_ZuI6z8.webp)
We have two subnet, private and public.
Security Group : sg-PublicALB
public subnet is internet facing so it handles all the traffic from internet, to enable it we add an inbound rule to allow all traffic by specifying IP address as 0.0.0.0/0 and port as 80 which is by default used for http and all the traffic will be handled by application load balancer and distrivuted accordingly to frontend servers.
As Security group have stateful nature, there is no need to specify outbound rule for reverting back the response to 0.0.0.0/0(ALL)
Security Group : sg-PublicEC2
EC2 serving frontend will only take request from sg-PublicALB and will hit to API which resides in private subnet so in inbound rules we specify source as sg-PublicALB and for outbound we specify the sg-PrivateALB
Security Group : sg-PrivateALB
In private subnet we have two security groups one for application load balancer that helps managing the traffic from frontend efficiently and safely, where as other security group is used to keep backend services secure.
So inbound rule for sg-PrivateALB would be only for traffic from sg-PublicEC2(frontend), and outbound will be only for sg-PrivateEC2
Security Group : sg-PrivateEC2
sg-PrivateEC2 will only allow traffic from sg-PrivateALB which have load balancer in it. It does’t have any outbound rules as it is the last processing node, and will revert back the response to same sg-PrivateALB specified in inbound rules.